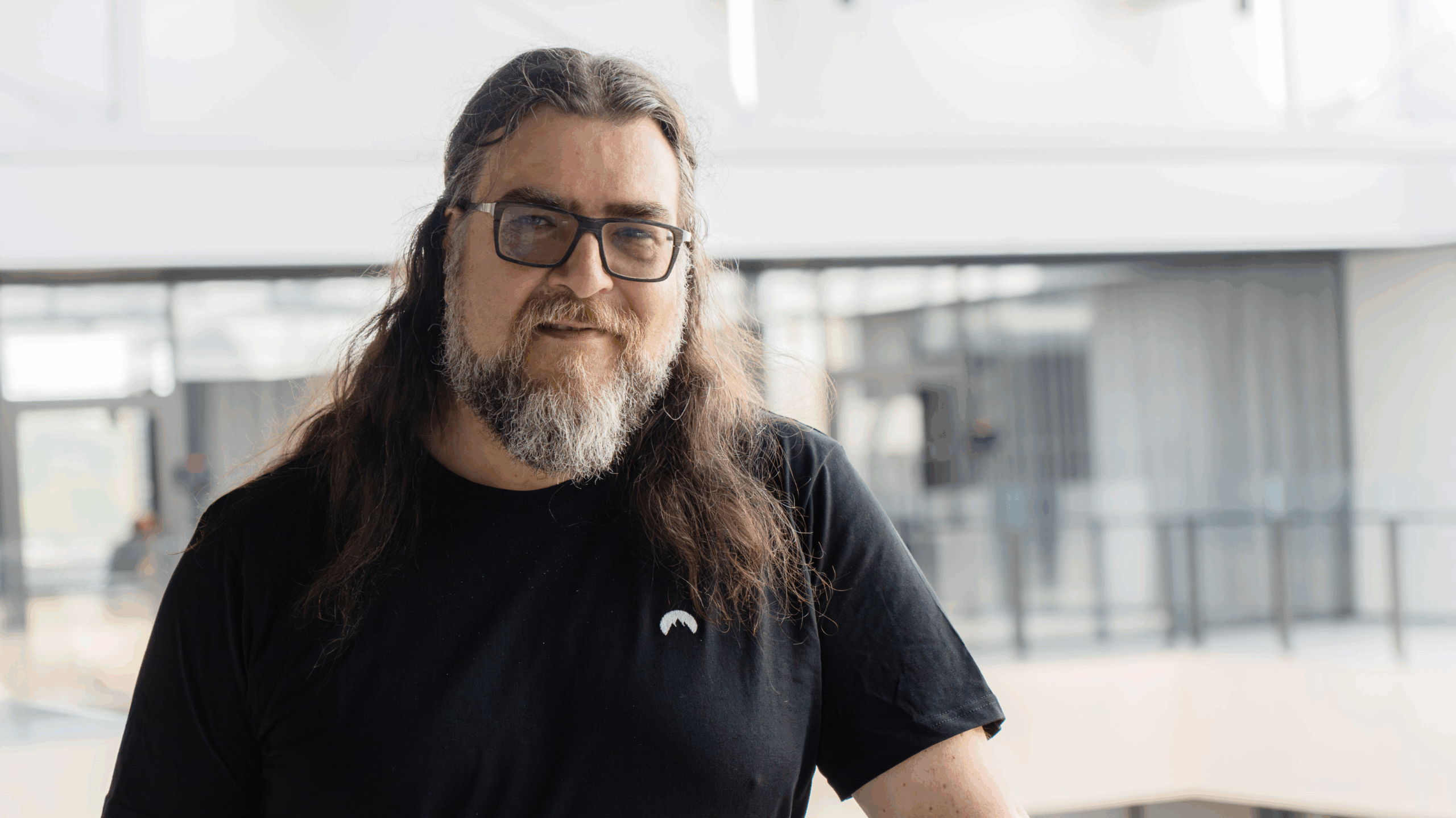
Michael Quinn, managing director of Cyber Risk at Kroll, tells Global Finance about corporate cyberthreats and how he helps corporate hacking victims investigate and develop response plans for digital attacks.

Global Finance: What kinds of digital attacks do you deal with?
Michael Quinn: We focus on incident response and computer forensics. If a company gets hacked, if there’s an intruder in the network, if email has been compromised, if there are concerns about unauthorized access—however it may have been—that’s typically when Kroll gets involved. We have teams covering EMEA, APAC, Latin America, and sometimes cases bleed over to different regions with companies that are global. But my focus is in the US.
We also help companies create or update their cybersecurity incident response plans. These should be somewhat general because even though there are similar types of compromises, there are always nuances that make each situation unique. A plan can’t speak to every type of incident.
GF: What’s the process to investigate a breach?
Quinn: We look at systems, collect data, review evidence forensically and then figure out how they got in, the tools they used, the earliest date of compromise and what we believe they accessed and/or took. Then we recommend how to fix that hole and document our findings so they can provide that to counsel as well as a government agency or law enforcement.
GF: What type of information are hackers typically going after?
Quinn: Corporate information is often way more valuable than Social Security numbers or email addresses. There are different attacker groups. One might be interested in intellectual property—to pirate the latest movie, for example. Another might want information about people who use a particular product or service.
GF: Do you ‘get’ bad guys? Can you identify the hackers?
Quinn: We don’t focus on attribution. We leave that to the government. But we’ll work with the government, provided our clients let us. Have we found information that leads us to believe that a hack has come from China, Russia, Eastern Europe, North Korea? Absolutely. Does that mean it absolutely came from those countries? No. It’s so easy to hide an IP address that it’s extremely difficult to attribute an attack to a country based on an IP address and toolset; toolsets are stolen and leaked. Attribution takes evidence collected by the FBI, NSA and other government agencies.
Right now, we’re seeing new regulations outside the US that will likely cause more companies to either manage their cybersecurity or invest more in it, or call in companies like us.
GF: What’s the cost of a hack to a business?
Quinn: An investigation involves us, attorneys and the company—who also have day jobs running the company. Sometimes, third-party e-discovery companies are hired when email is hacked. They look for sensitive information that could drive regulatory notifications, GDPR issues, etc. Not all email is digital or readable by the computer, making it a lengthy review, likely conducted by attorneys. Overall, costs go beyond legal, forensics, e-discovery and PR; there are reputational and business interruption costs too.
GF: What best practices do you recommend?
Quinn: Enable two-factor authentication on every account and use a password manager. Make sure that personal and/or business phones have passwords set up such that attackers can’t call your service provider to ask to port your SIM to another phone and receive your calls. Also, I would almost always recommend against employees using their own devices.
GF: Is it better to come clean or keep quiet about hacks?
Quinn: [US] regulation requires companies to look into and disclose cybersecurity issues. A company also needs to follow through because people who were affected want to know what happened, how the company fixed it so it won’t happen again and what the company will do to make people whole again.